Key Benefits
See how IntelliSec breaks the mold — comparing typical MDR, XDR & SIEM vendors against what we actually deliver.
Typical Vendors
MDR • XDR • SIEM
Restricted OS Support
Agents often require specific Windows versions or enterprise Linux distros, leaving FreeBSD, older OS builds, and mixed environments unmonitored and exposed.
Walled-Garden Dashboards
You are forced into their proprietary portal. Integrating with your existing SIEM — Splunk, QRadar, Elastic — requires heavy licensing upgrades or is simply not possible.
Generic, One-Size Rules
Detection rules are vendor-owned and standardized. Custom logic requires months of professional-services engagements, at extra cost, and rarely applied per-client.
Locked-in AI Engine
You use their AI model — or none at all. Bringing your own LLM, switching providers, or running a private air-gapped model is not on offer.
Vendor lock-in • Rigid deployment • Zero customization
The IntelliSec Way
Built for Freedom & Control
Universal OS Coverage
Our lightweight agents run on virtually any Windows, Linux, FreeBSD, and macOS version — from modern servers to legacy endpoints — leaving no blind spots.
Your Dashboard, Your Rules
Use the powerful IntelliDashboard out of the box, or feed data directly into your preferred SIEM — Splunk, Elastic, QRadar, or any other — via native integrations.
Per-Client Custom Rules
We write and deploy bespoke detection rules tailored to each client's environment, industry, and threat profile — giving you coverage no generic ruleset can match.
LLM of Your Choice
Leverage our battle-tested IntelliLLM for AI-augmented threat analysis, or plug in your own preferred LLM — on-prem or cloud — without changing anything else.
No vendor lock-in • Secure & easy deployment • Fully customizable
No Vendor Lock-in
Your data, your tools, your rules. Swap components at any time without rebuilding your security stack from scratch.
Easy & Secure Deployment
Lightweight agents deploy in minutes across heterogeneous environments. All data stays encrypted on-prem — fast, safe, and scalable.
Fully Customizable
From detection rules to dashboard and AI engine — every layer is adjustable to your organization's unique needs and preferences.
How IntelliSec Works
Lightweight agents on your endpoints write encrypted IntelliSnapshot files, which are processed by the Core System that makes the smart security conclusions and renders everything in a very human-friendly alerts in IntelliDashboard.
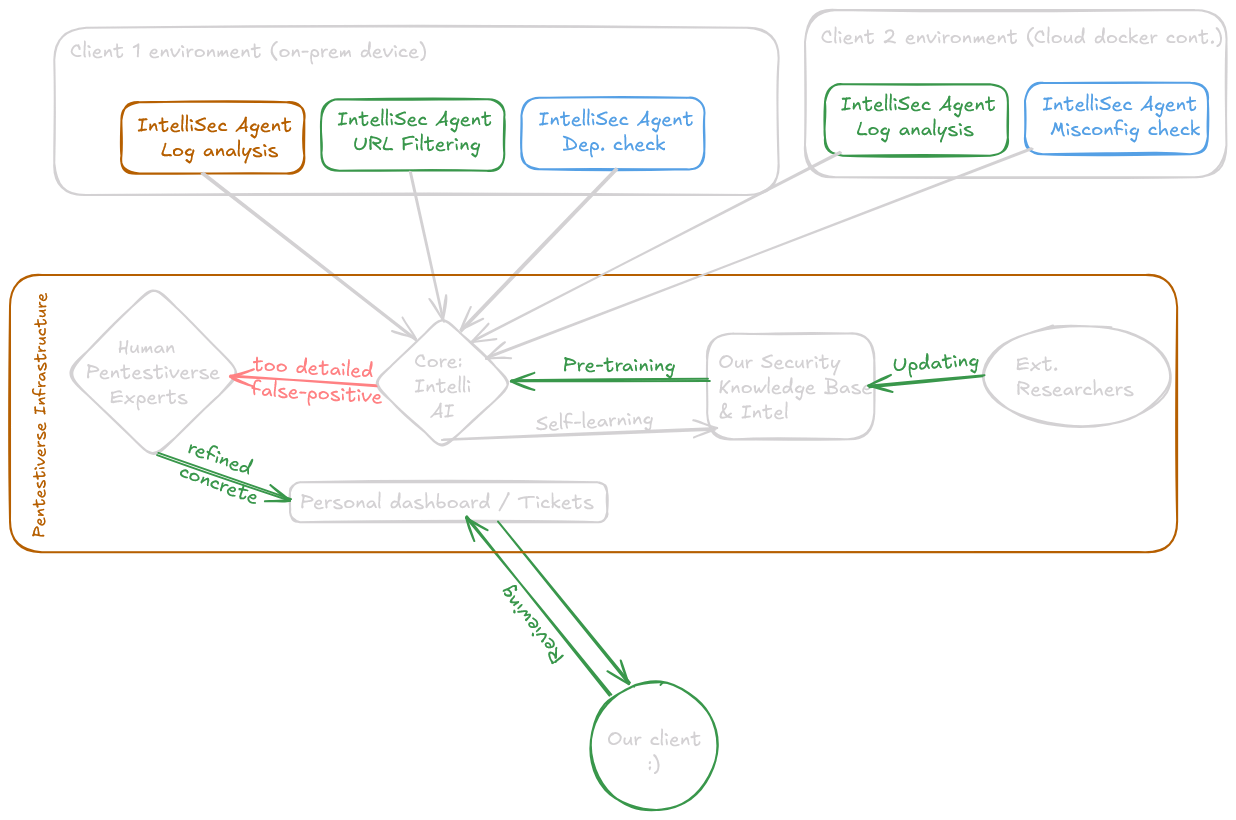
Scalable Agents
Once deployed, lightweight agents start collecting relevant security data from your endpoints safely and saving it locally encrypted in a secure snapshot file. This allows us to scale and handle one or millions of endpoints with minimal performance impact.
LLM as a consultant
We don't trust LLM's just enough to allow them to do decision making for your business, but we trust ours enough to help in augmenting and explaining vulnerabilities that our team trained it on.
Security Expert Support
When dashboard alerts are not enough, our security experts are available on-demand to help you interpret complex findings, recommend remediation steps, and provide guidance on improving your overall security posture.
Technical Specifications
What IntelliSec Monitors
Every organization faces different threats. During onboarding, you will use a checklist to define which security domains matter most for your business. The version that is deployed will then monitor those specific areas in depth:
Vulnerability Intelligence
We correlate endpoint configurations, installed software versions, and patch levels against known vulnerabilities from CVE databases to identify exploitable weaknesses and inform you near real-time. Isn't that cool?
Proactive DefenseApplication & Permission Control
Track every software installation, monitor blacklisted applications, detect suspicious permission escalations, identify unsigned drivers with complete endpoint software visibility.
Endpoint GovernanceNetwork & OS Integrity
Analysis of suspicious network activity, unauthorized open ports & services, and OS integrity checks to detect rootkits.
Data Loss PreventionCompliance & Audit Readiness
Automated compliance checking against CIS Controls and NIST Cybersecurity Framework. Augmenting our agents with compliance-specific monitoring rules to help you stay audit-ready.
CIS & NISTForensic-Grade Logging
Deep system log analysis, security event correlation, and forensic trail maintenance. Human-friendly correlation per user, time, and endpoint to facilitate investigations.
Incident ResponseCustom Security Policies
You can inform us of any custom security policies or compliance requirements during onboarding, and we will build monitoring rules tailored to your organization's needs.
Your Rules, Your WayPricing & Compliance
Flexible subscription model with enterprise discounts and compliance-ready monitoring
Subscription Pricing Starting
per endpoint, per month
Billed monthly. Yearly commitment benefits apply.
- Custom-built agents with YOUR selected security rules
- Isolated infrastructure per client (Core, LLM, DB, Dashboard)
- Periodic monitoring with 5-minute collection cycles
- LLM-powered augmentation with NIST/CIS context
- Expert security team support for critical findings
Volume Discounts:
Compliance & Standards
CIS Benchmarks
Center for Internet Security baseline compliance
NIST Framework
Cybersecurity Framework implementation
IntelliSec agents continuously verify your endpoints against CIS Benchmarks and NIST Cybersecurity Framework requirements. We provide you a detailed report highlighting compliance status, gaps, and remediation recommendations to help you stay audit-ready.
Supported Certifications:
Translating complexity.
Into human-friendly actions.
Having Intellisec frees your business to depend on vendors that want to control your data.
Book Your Free Coordination Call
No sales pitch. No obligation. Just a 15-minute conversation with Pentestiverse security expert about your threat landscape, compliance gaps, and how custom endpoint intelligence can address your specific challenges.